Data Breaches: Aspects of emotional and behavior turmoil
It has become almost commonplace to open up your favorite news site, pick up the newspaper, or listen to the evening news to find out that yet another company has experienced some type of electronic intrusion. The conversations about these “hacks” seem to proceed through an emotional hierarchy not unlike that experienced during other stressful life events such as divorce or loss of job.
Shock or Disbelief
We hear about a major organization that has been breached and the first question we ask is “How can a company that size not have the knowledge and capability to protect their data?” We ask this question because most of us are under the impression that really smart people work for multi-billion dollar organizations, and we think that because they can distribute products to and sell from thousands of brick and mortar locations or websites; we can’t imagine how they don’t have their data security fully buttoned up.
Denial
This emotion is triggered by our defense mechanisms. Our cerebral cortex immediately kicks into high gear and we begin to base our denial on irrational rules e.g. “I’m safe because I haven’t shopped there in a year.” How did we come up with the decision that we are safe because we haven’t shopped there in a year? There is no doubt in my mind that if it was 6 months since we had shopped there, our rational would be that this was the safety threshold. Regardless, our instincts for survival start to set off these background alarms and we anxiously scour the Internet for news stories that confirm our irrational thought process. Eventually, after a period of investigation, the breached company surfaces with a report either confirming or contradicting our rational. At this point, the foolish among us actually give a sigh of relief; only to have a second report issued one month later indicating that the company’s subsequent study determined that twice as many individuals’ datum were breached.
Anger and/or Fear
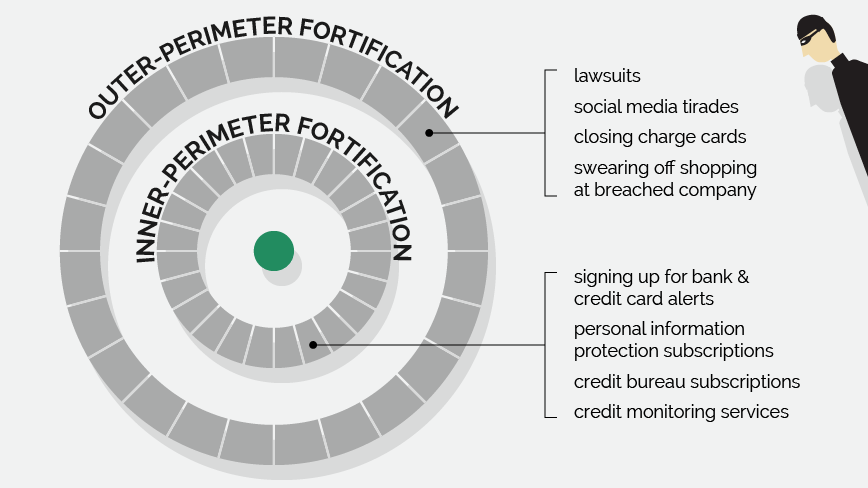
These are both the first “reactionary drivers”. This is the stage we enter once we can no longer rationally or irrationally deny the possibility that we have been affected. These are emotions that drive us to take action that in our minds will present a fortification or wall against being damaged or hurt. There are two forms of action that we take.
Outer-perimeter fortification” and “Inner-perimeter fortification.”
Surrender and Hope
This is the second stage of irrational thought. This stage is preoccupied by an acceptance that:
- There could be clear and present danger that is the result of the actions of the breached organization
- The ability to defend one’s self against these dangers is out of the individuals’ control
- The individual begins to extend their thought process in search of the steps that would be needed to perform remediation once the danger materializes and damage is measurable
- The individual hopes for two things:
- Damage can be managed to a minimum
- The breached organization will support the individual in their efforts to remediate damages
Three Data Breach Cases: What were the responses?
As the occurrences of corporate data breaches have increased, we have seen how the reaction on the part of the breached company has changed over time. In 2006 TJX, the parent company of retailers such as TJX and Marshalls, was hacked. It took more than a year for the company to realize that it was hacked, and when it did, it had to revise the reported effects of the hack multiple times until finally concluding that more than 47 MM credit cards were compromised.
An indication of how TJX responded was evidenced in the January 2007 article published by CNet. “We think it’s a little odd that they would characterize themselves as victims when it appears that they may have been capturing data that is unnecessary,” said Daniel Forte, chief executive of the Massachusetts Bankers Association. TJX eventually settled with each of the 42 state attorneys general for approximately $9.5 MM.
The next case we will discuss is the data breach that took place at Target during the holiday shopping season of 2013.
During that holiday shopping season, approximately 40 million consumers had their credit and debit card numbers stolen; approximately 70 million other Target customers also had their personally identifiable information (PII) pilfered.
The result of this was dramatic. As of February 2014, Target had spent $61 MM in legal fees, software enhancements, customer reimbursements and credit monitoring, and other costs due to the failure to protect customer data, the Washington Post reported. This is not to mention the many personal lawsuits that had yet to be settled.
But, the fallout over this has not been fully measured. Their data breach eroded customer trust, which was demonstrated in Target’s sales numbers that dropped almost 50% after the breach the Washington Post reported.
A subsequent study done by Annalect’s research team confirms the lessons learned from the Target data breach: Data breaches result in a loss of confidence and modified spending habits. The study indicated that 72% of consumers say that their perception of the retailer/company changed for the worse, and that 12% of consumers say they’ve stopped shopping at the retailer/company where a data breach occurred.
Lastly, there is the case of Anthem Insurance, the largest for-profit, managed healthcare company in the Blue Cross and Blue Shield Association, who was hacked in 2014. This hack resulted in the theft of Personally Identifiable Information of more than 78 MM people across 14 states. What was particularly interesting was that adding to the company’s woes, it was accused of failing to inform customers of the breach, which led to an investigation by a number of attorneys general from various US states. While the courts have not yet proven this, Anthem decided to take the bulls by the horns and get ahead of the fallout. Anthem directly contacted each of the individuals whose data was stolen, informing them that they were being provided $2MM of insurance against losses, as well as, automatic enrollment with an information and credit management company. Then to take it a step further, they assured each of the affected customers that in the event that there was damage to their credit, a service representative would work hand-in-hand with the customer in order to assure that their credit history and rating were repaired.
Why did one company respond so differently than the others?

Had lessons been learned from all of the data breaches that had occurred between the TJX breach and the time when their own breach occurred? What had changed during that 10-year span? Was it the attitude of one industry versus another? Was it possible that the growth of awareness and power of social media impacted the urgency of a response?
Data Breach Responses: Make it personal…take it to the people
“It’s not personal, its business” — Sonny Corleone (The Godfather, 1972)
A mere 15 years ago, the spring bud of social media had not even exposed itself, and the concept of corporate business cyber intrusions had not been conceived (at least not from the perspective of private information theft). Corporations had been operating behind a protective barrier that shielded them from having to react to public outcry and response without first waiting and taking a good amount of time to study the long-term effects of negative publicity, counting on Joe Public’s notorious reputation for having a very short memory. In a 15-year period, the need for direct engagement with the public has been driven by the growth and adoption of social media. This shift in paradigm has created a maelstrom for corporations. It has forced corporations to refocus on the humanistic side of how businesses must deal and effectively manage public opinion, behavior, and response to negative events such as corporate cyber intrusions that have direct negative impact on the human condition.
The ability of corporations to design their responses to cyber intrusion in order to align with the emotional phases mentioned in section I, could be the difference between paralyzing financial and reputation damage versus maintaining the status quo or even growth of the brand.
A looming question is whether all customers of a company that have experienced a cyber-intrusion require the same level of attention of direct engagement, or are there enough differences that would require varying approaches, themes, and methods of engagement?
In order to gain better insight into these potential differences, we conducted a poll that worked to understand the differences across 3 demographics:
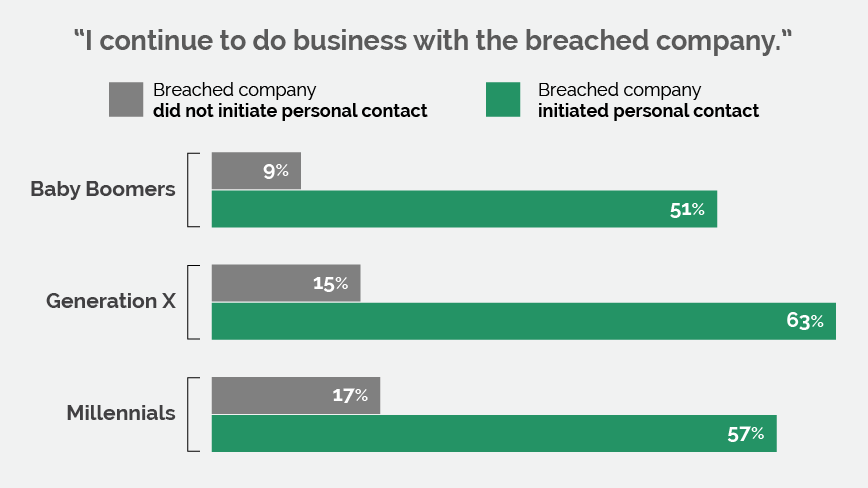
While there are subtle differences, the poll results are conclusive and undeniable. The human need for personal attention, especially during periods of stress brought on by a data breach, should be recognized by all companies.
This recognition should be translated into what I will refer to as their “Brand Disaster Management Strategy.” The one that will be required to save their brand when – not if – the time comes that they are breached.
Conclusion
While we often hear references about the fact that social media has numbed the need for direct social interaction, the human condition demands human interaction during times of need. We come together, cluster, collaborate, and commiserate. It is something that has been cultivated over the last 4–7 million years (Hominins and other Hominoidea). It is highly doubted that 10 years of social media is about to undo millions of years of cultivation of the human condition.
The recognition of the human condition is something that must be carefully considered by companies in the development of their “Brand Disaster Management Strategy”. The one that will be required to save their brand when – not if – the time comes that they are breached.
The data for this survey was collected in poll format using SurveyMonkey. There was a total of 946 respondents within Omnicom Group, across a variety of demographics.